Home / Blog / Web Development
Node.js Security: 10 Essential Code Snippets to Protect Your Backend

Introduction
Truth be told, the majority of Node.js apps are not hacked because of sophisticated attacks. They are compromised due to mere security vulnerabilities such as unverified input, weak authentication or revealed secrets.
That is why Node.js security is not only a best practice, but a must.
This guide contains useful copy and paste fragments of code that ensure that you protect your backend without complicating matters. No theory overload, just what works in real projects.
Here’s what we’ll cover:
- Locking down authentication and JWT usage
- Preventing SQL injection and XSS attacks
- Securing data with proper hashing and encryption
- Setting up HTTP headers and CORS correctly
- Protecting your app with rate limiting and monitoring
We’ll also highlight real security incidents and the lessons developers learned the hard way, so you don’t have to.
If you want to build Node.js applications that are not just functional but secure by design, this is a solid place to start.
Why Node.js Security Matters
It is easy to think that your app is safe until you read about how even secure systems are exposed by minor security lapses.
In early 2024, the Node.js team announced various high severity security defects (such as HTTP request smuggling bugs) that can provide attackers with an opportunity to interfere with how servers handle requests. Practically, this implies that a malicious attacker may be able to slip unscrupulous requests under your defenses even when your application logic does seem correct on the surface.
This is a reminder that the security of Node.js is not necessarily only about your code, but also about the very manner of how your system is set up and performs under the real traffic conditions.
Turn Security Gaps Into Fortified Node.js Apps
Protect your backend from threats, vulnerabilities, and data breaches. Debut Infotech delivers bulletproof Node.js security, scalable, compliant, and battle-tested.
Why This Happens in Node.Js Architecture
The strength of Node.Js Architecture, its asynchronous, non-blocking nature, is also where risk can creep in:
- Your app handles many concurrent requests, increasing exposure
- It depends heavily on third-party packages
- It continuously takes in untrusted user input.
The combination of the two makes Node.js fast and scalable, though it also implies that even minor gaps may easily turn into significant vulnerabilities.
Common Security Risks Developers Face
In real life projects, the following issues are recurrent:
- Injection attacks
Attackers are able to tamper with backend logic or database queries when they are not validated.
- Broken authentication (JWT mistakes)
As an illustration, allowing unreliable tokens or not verifying them appropriately can allow the attackers to log in as any user.
- Wrongly configured headers and HTTP processing.
Lack of security headers or wrong request parsing can make your app vulnerable to such attacks as request smuggling or data leakage.
What This Means for You
Here’s the honest truth:
Most security problems in Node.js apps don’t come from advanced hacking,they come from everyday shortcuts and assumptions.
- “This input looks safe”
- “We’ll secure it later”
- “The framework handles that”
Sadly enough, attackers take advantage of the very assumptions.
This is why security should not be an accidental part of the process, but a sensible approach to creating a reliable and production-ready application that will not crumble when you put it to the test.
Essential Node.js Security Code Snippets
In the case of creating a Node.js secure api, security is not about employing dozens of tools, it is about getting the basic right. These are the actual trends that experienced developers use in practical projects regardless of whether the project is based on a modern Node.js framework or from scratch.
Let’s walk through the essentials you should never skip.
1. Validate Input Early
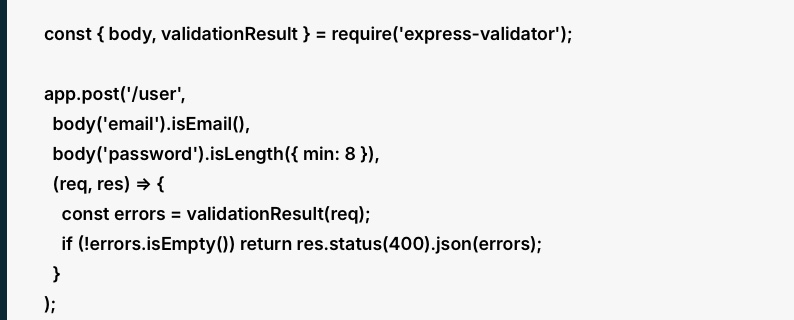
const { body, validationResult } = require(‘express-validator’);
app.post(‘/user’,
body(’email’).isEmail(),
body(‘password’).isLength({ min: 8 }),
(req, res) => {
const errors = validationResult(req);
if (!errors.isEmpty()) return res.status(400).json(errors);
}
);
What this does
This validates the request which comes in and before the application process is carried out. In this example:
- body(’email’).isEmail() makes sure the email field looks like a valid email address
- body(‘password’).isLength({ min: 8 }) ensures the password is at least 8 characters long
- validationResult(req) collects any validation errors
- In case of any mistakes, the API will give a 400 Bad Request.
Why it matters
Any request that comes to your API must be considered untrusted. Attackers make unpredictable/malicious input in an attempt to:
- break your application logic
- bypass business rules
- introduce malicious information into your database
- cause vulnerabilities in downstream systems.
The first checkpoint is the validation. It minimizes risk before the data hits on your controllers, services and your database.
Practical takeaway
A good validation enhances security as well as reliability. It is not only able to block attacks, but it ensures that your app does not process bad data later on which would create bugs.
2. Hash Passwords Securely with bcrypt
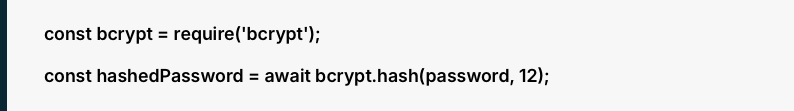
const bcrypt = require(‘bcrypt’);
const hashedPassword = await bcrypt.hash(password, 12);
What this does
Instead of storing the original password, this converts it into a hashed version. A hash is a one-way conversion which implies that you do not keep the actual password in your database.
The 12 is the salt rounds value. The amount of work done by bcrypt to create the hash is controlled by it.
Why it matters
In the event that your database gets exposed, plain-text passwords would automatically expose users to danger. Hashing makes stolen password information much more useless to attackers.
There is also automatic addition of salt in bcrypt, which functions to prevent rainbow table attacks as well as to ensure that similar passwords produce different hashes.
Practical takeaway
Hashing is not optional for user passwords. Storing passwords in plain text and using weak hash functions is one of the most harmful mistakes in real systems, and bcrypt can be considered a trusted and well-utilized solution.
3. Use JWT Authentication with Expiry
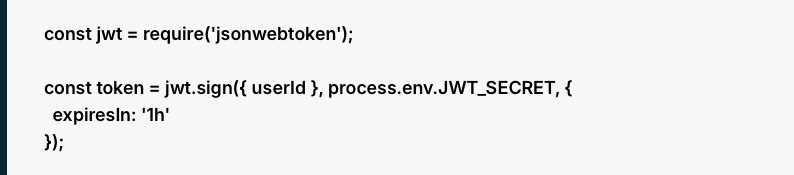
const jwt = require(‘jsonwebtoken’);
const token = jwt.sign({ userId }, process.env.JWT_SECRET, {
expiresIn: ‘1h’
});
What this does
This generates a JSON Web token of the user. The token includes:
- a payload, in this case, with user id.
- a secret key from your environment variables
- an expiration time of 1 hour
The future requests can then be authenticated with the help of the token.
Why it matters
JWTs are extensively used since they render the process of authentication to be scalable and versatile. However, they may be risky when managed improperly.
When a token does not have an expiration date, any person that steals it can have access without limit. This is the reason why expiresIn: ‘1h’ is significant. It restricts the harm in case a token is breached.
Practical takeaway
JWTs are useful, but they are not secure by default. You still need to:
- set short expiration times
- protect the signing secret
- avoid exposing tokens carelessly
- consider secure storage methods, such as HTTP-only cookies where appropriate
This constitutes a large portion of learning to secure api in Node.js in actual deployments.
4. Add Secure HTTP Headers with Helmet
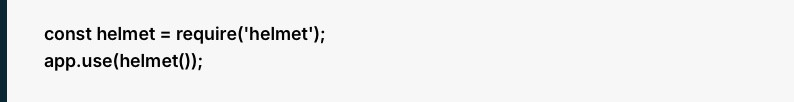
const helmet = require(‘helmet’);
app.use(helmet());
What this does
Helmet is a middleware which automatically appends a number of security related HTTP headers to your responses. These headers help protect against issues such as:
- XSS-related browser risks
- clickjacking
- MIME-type sniffing
- some unsafe browser behaviors
Why it matters
Browsers do not display content, they understand it. In the absence of protective headers, an attacker can take advantage of the way a browser manages the response of your application.
Helmet provides a good default setup which does not require writing every header manually.
Practical takeaway
This is among the simplest yet proven security enhancements that you can be able to add to an Express app. It is less complicated, easy to use, and provides significant protection without configuration.
5. Add Rate Limiting
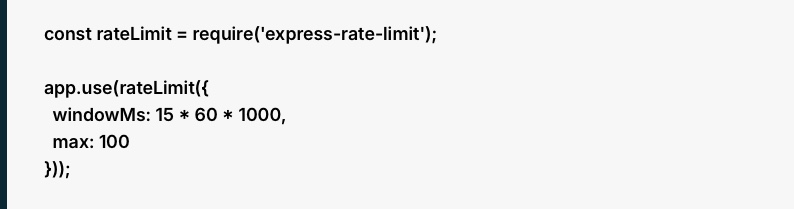
const rateLimit = require(‘express-rate-limit’);
app.use(rateLimit({
windowMs: 15 * 60 * 1000,
max: 100
}));
What this does
This restricts the number of requests that a client could make within a time window.
In this example:
- windowMs is 15 minutes
- max is 100 requests during that period
When a user surpasses such a limit, the server will drop subsequent requests until the time window restarts.
Why it matters
Rate limiting is used to curb abuse. Particularly it is helpful in the protection of:
- login routes from brute-force attempts
- public endpoints from spam
- APIs of simple denial-of-service style abuse.
Without rate limiting, attackers will be able to hit your endpoints as many times as they can and flood your service or guess credentials.
Practical takeaway
The rate limit should not be the same on all routes. General read-only endpoints can have significantly less restrictive limits than login, password reset, OTP and signup endpoints.
6. Sanitize User Input
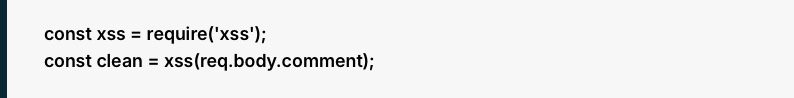
const xss = require(‘xss’);
const clean = xss(req.body.comment);
What this does
This eliminates or disarms potentially harmful HTML or scripting messages posted by users.
When somebody posts some malicious JavaScript in a comment box, the process of sanitizing prevents the subsequent presentation and execution of that script in a web browser.
Why it matters
Sanitization and validation are not similar.
- Validation verifies that the input is in the correct format.
- Sanitization filters unsafe material on otherwise good input.
As an example, a comment can be a valid text but include malicious script tags. Sanitization assists in addressing that danger.
Practical takeaway
This is particularly necessary with the kind of content generated by users themselves, including:
- comments
- profile bios
- reviews
- forum posts
- support messages
When your app receives text which might be later posted or shown elsewhere, then sanitization needs to be a part of your process.
7. Protect Secrets with Environment Variables
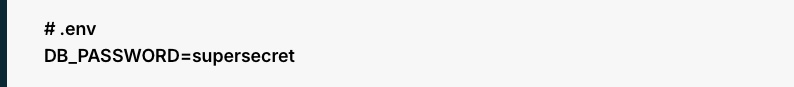
# .env
DB_PASSWORD=supersecret
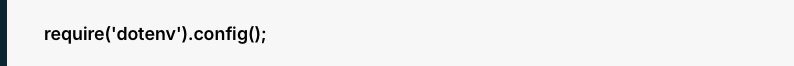
What this does
Instead of hardcoding credentials directly in your source code, this stores them in environment variables and loads them into your application.
Examples of secrets include:
- database passwords
- API keys
- JWT secrets
- credentials of third-party service.
Why it matters
One of the most popular security errors in the domain of backend development is hardcoded secrets. When code is uploaded to some public repository or shared in some irresponsible manner, such secrets can be revealed instantly.
Isolating secrets from the code ensures that deployment is more secure and adaptable to environments such as development, staging and production.
Practical takeaway
In mature custom software development environments, teams sometimes go to the next stage and use special secret managers rather than just using .env files. Nevertheless, environment variables remain a significant minimum requirement.
8. Prevent SQL Injection with Parameterized Queries

db.query(‘SELECT * FROM users WHERE email = ?’, [email]);
What this does
This transmits the query and the input individually, rather than putting them in a single raw string.
The input is accepted by the database as data and not as a runnable SQL code.
Why it matters
SQL injection occurs when the input that is controlled by the attacker is directly inserted into a query and it modifies its meaning.
An example of this is that, when you construct queries by concatenation of strings, a malicious user can inject SQL commands that:
- bypass login checks
- read private data
- modify or delete records
That is avoided by parameterized queries which maintain structure and data apart.
Practical takeaway
You must know this principle even when you are using an ORM. A significant number of security problems occur when developers leave ORM protection or craft raw queries in an irresponsible way. This belongs in every secure tech stack for web development.
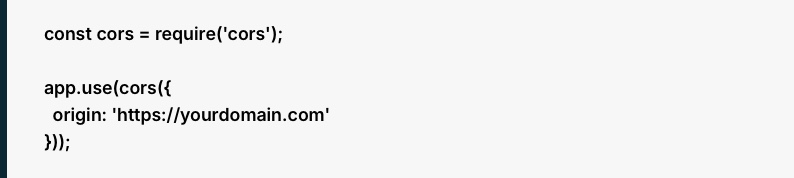
9. Configure CORS Properly
const cors = require(‘cors’);
app.use(cors({
origin: ‘https://yourdomain.com’
}));
What this does
CORS is used to determine the external sources that may make requests to your API using a browser.
In this example, only requests coming from https://yourdomain.com are allowed.
Why it matters
When CORS is excessive, other websites could be able to communicate with your API in an unintended way. This may cause a higher risk, particularly where credentials or endpoints of sensitivity are at stake.
One of the weak setups that is commonly used is to allow all origins with an * even during production.
Practical takeaway
CORS is not a substitute for authentication but it is a significant browser level protection. It must be set in a controlled manner depending on which frontend domains you actually have trust in.
10. Add Logging and Monitoring
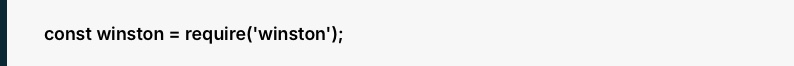
const winston = require(‘winston’);
What this does
Mechanisms such as Winston assist you record application activity, errors, warnings, and suspicious events. This can include:
- failed login attempts
- repeated 401 or 403 responses
- unusual spikes in requests
- server errors
- security-related events
Why it matters
Security is not merely a matter of prevention. You also need visibility. A lot of teams find out about an incident too late because they did not document the warning signs in a manner that is understandable. Good logging helps you:
- identify abnormal behavior.
- explore issues more rapidly
- improve incident response
- get an idea of what went wrong following a failure.
Practical takeaway
Logs must be practical, designed and safe. Logging sensitive data such as raw passwords, tokens and secret keys should be avoided.
Worried About Node.js Vulnerabilities? Let’s Talk.
Our security experts audit, harden, and future-proof your Node.js architecture. Free consultation, actionable insights.
Why Debut Infotech Is a Smart Choice for Secure JavaScript Development
The development of a secure backend is not only a matter of having the appropriate tools or libraries, but also using them in a proper manner and in a unified way throughout your whole system.
This is in fact where numerous teams fail. Security is typically relegated to the later development stages, when addressing the problem becomes more costly, time-intensive, and threatening.
Debut Infotech is a reliable Node.js development company with a different approach.
We do not consider security as an afterthought; we make it part of any given application. Security decisions are made early when they are needed the most, such as authentication and API design, data handling and deployment.
The difference is our practical experience.
We have experienced how vulnerabilities in the real-world manifest in the production environment be it weak validation, bad token management and poorly configured APIs. That experience enables us to come up with systems that avoid issues before they happen rather than the ability to respond to such issues later.
Maintainability is another aspect that is important.
Security must not slow your team or introduce a complexity. Debut Infotech specializes in developing solutions that are secure and practical, so that your developers can work effectively and, at the same time, maintain high standards of security.
At the end of the day, secure applications don’t happen by accident.
They are the outcome of deliberate choices at the very beginning and throughout the course of time. Having collaborators is the key to the enhanced level of reliability and trust of your Node.js applications, and partnering with a team that values security throughout your development lifecycle can be a decisive factor.
Frequently Asked Questions (FAQs)
A. Node.js is a secure platform, but it isn’t “locked down” by default. Although the basic system is secure, its actual vulnerabilities typically lie in the way a developer constructs the application and the third-party npm packages that they opt to use.
To ensure that an application is safe, you need to take proactive measures to manage it. This implies routinely auditing dependencies on vulnerabilities, purifying all user data to prevent injections, and not using root privileges to minimize the possible harm. Finally, Node.js offers a good base, yet its real security will rely on the standard best practices in its implementation.
A. Yes, Node.js applications can be hacked.
Node.js is typically secure itself, although the vulnerabilities are typically related to the construction and maintenance of applications. Most security problems are due to either insecure coding or a high degree of dependency on third parties or improperly configured servers and APIs.
In simple terms, Node.js is not a problem, how it is used today is what makes your application secure.
Our Latest Insights




