Home / Blog / Coin Development
Token Lifecycle Explained: Stages, Benefits, and Real-World Use Cases

The token lifecycle refers to the complete path a token follows from creation to retirement, encompassing stages such as issuance, active use, updates, state changes, and eventual deactivation. This concept is central to secure transaction processing, identity management, and digital asset handling.
As digital ecosystems expand, managing the token lifecycle becomes essential for resilience and compliance. By 2025, an estimated 35 % of global transactions are expected to be tokenized, reflecting widespread adoption of token-based security models.
Additionally, more than 70% of financial institutions report reduced fraud after implementing token technologies, underscoring their value in protecting sensitive data.
Design a Smarter Token Lifecycle
Work with a team that understands how tokens behave in real systems. We map every stage properly, from provisioning to deletion.
What Is a Token Lifecycle?
A token lifecycle defines the complete journey of a digital token, from its conceptual design to post-circulation governance. It begins before issuance, with asset or rights mapping, legal classification, and economic modeling that determine what the token represents and how it can be used. The lifecycle then moves into architecture design, where standards, transfer rules, and control mechanisms are fixed.
At this stage, token minting defines how and when tokens are programmatically created on-chain, including supply limits and issuance conditions. Once minted, tokens are distributed through eligibility checks, custody models, and compliance gates.
During circulation, tokens undergo state changes such as locking, staking, redemption, or restricted transfers, often without moving wallets. Eventually, tokens are redeemed, consumed, burned, or archived. Even after retirement, auditability, reporting, and governance obligations continue, making the lifecycle an ongoing operational process, not a one-time event.
Key Stages in the Token Lifecycle
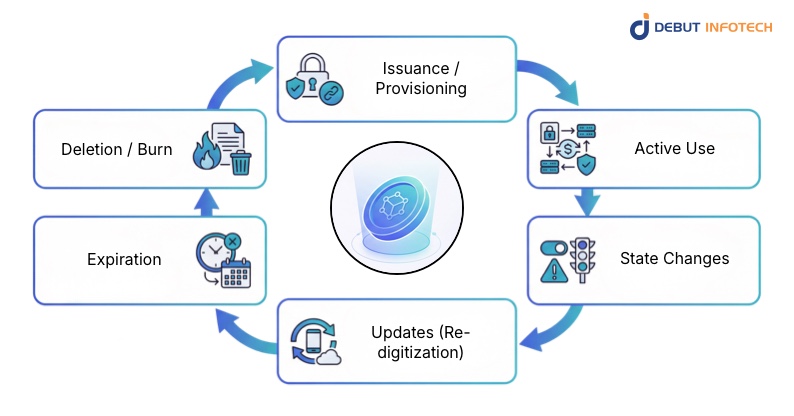
Every token follows a defined lifecycle that governs its issuance, use, updates, restrictions, and retirement. Each stage plays a specific role in maintaining security, reliability, and operational continuity.
1. Issuance / Provisioning
Token Issuance/provisioning involves creating a token and securely linking it to an underlying asset, identity, or payment credential. Strong provisioning processes verify ownership, apply security rules, and ensure tokens are issued only through trusted channels. This step sets the foundation for trust and long-term usability.
2. Active Use
During active use, tokens function as substitutes for sensitive data in transactions, authentication flows, or asset interactions. They enable day-to-day operations while keeping underlying credentials protected. This phase supports scalability and consistent performance across platforms and environments.
3. State Changes
Tokens can shift states based on risk signals or business rules. They may be suspended, reactivated, or restricted temporarily. State management allows systems to respond quickly to account changes, fraud indicators, or compliance requirements without disrupting legitimate usage.
4. Updates (Re-digitization)
Re-digitization refreshes a token when underlying details change, such as a card re-issuance token or device upgrades. Updates happen without user interruption, preserving continuity. This capability supports long-term token reliability while reducing failed transactions and the need for manual intervention.
5. Expiration
Tokens are assigned defined validity periods. Expiration ensures that outdated or unused tokens are automatically invalidated. This reduces security exposure and helps organizations maintain clean token inventories aligned with internal and regulatory policies.
6. Deletion / Burn
At the end of its lifecycle, a token is permanently removed or cryptographically burned. Token burning ensures it can no longer be reused or recovered. Proper deletion closes the lifecycle securely and prevents residual risk.
Benefits of Token Lifecycle
A structured token lifecycle delivers measurable business and security benefits by reducing payment failures, improving transaction reliability, and enabling precise control over how sensitive data is accessed and protected.
1. Reduced Involuntary Churn
Token lifecycle management helps prevent service disruptions caused by expired cards, reissued credentials, or account updates. Tokens can be refreshed automatically without customer involvement, keeping payments active. This continuity reduces failed transactions, avoids unnecessary subscription cancellations, and supports stable recurring revenue while maintaining a smooth customer experience across billing cycles.
2. Enhanced Transaction Security
By replacing sensitive data with controlled tokens, lifecycle management significantly reduces the risk of fraud and data breaches. Tokens can be suspended, updated, or revoked instantly when risks are detected. This structured control limits attack surfaces, strengthens incident response, and ensures sensitive credentials remain protected throughout their usable lifespan.
3. Improved Authorization Rate
Well-managed tokens stay current with underlying credential changes, which lowers the likelihood of transaction declines. Authorization success improves because outdated or invalid payment details are removed from the flow. Over time, this consistency supports higher conversion rates, better checkout performance, and stronger trust between users, merchants, and payment networks.
4. Seamless Cross-Device Experience
Token lifecycle management allows tokens to function securely across multiple devices without exposing original credentials. Users can switch phones, browsers, or platforms while maintaining access and payment continuity. Device-specific controls still apply, ensuring security policies remain enforced while users experience uninterrupted service and consistent functionality.
5. Granular Security Control
Lifecycle management enables precise control over how, where, and when tokens can be used. Organizations can define limits by device, channel, geography, or transaction type. This fine-grained oversight supports risk-based decision-making, improves alignment with compliance requirements, and enables security adjustments without impacting legitimate usage or system performance.
Token Types
Different token types are designed for specific environments and use cases, balancing security, performance, and usability based on where and how tokens are stored and accessed.
1. Server-Based Tokens
Server-based tokens are generated, stored, and managed within centralized, secure environments. They support large-scale operations by enabling consistent monitoring, updates, and revocation from a single control layer. This model suits enterprises that require high availability, strong governance, and seamless integration across multiple platforms and services.
2. COF (Card-On-File) Tokens
COF tokens are designed for merchants that store payment credentials for future use. They support recurring billing, subscriptions, and faster checkout flows. By replacing stored card data, COF tokens reduce compliance exposure, lower breach risk, and maintain payment continuity when cards are updated or reissued.
3. Device-Based Tokens
Device-based tokens are bound to specific hardware, commonly used in mobile wallets and contactless payments. Each token is linked to a single device, adding an extra security layer. Even if compromised, the token cannot be reused elsewhere, making this type effective for consumer-facing payment applications.
Use Cases of Token Lifecycle Management
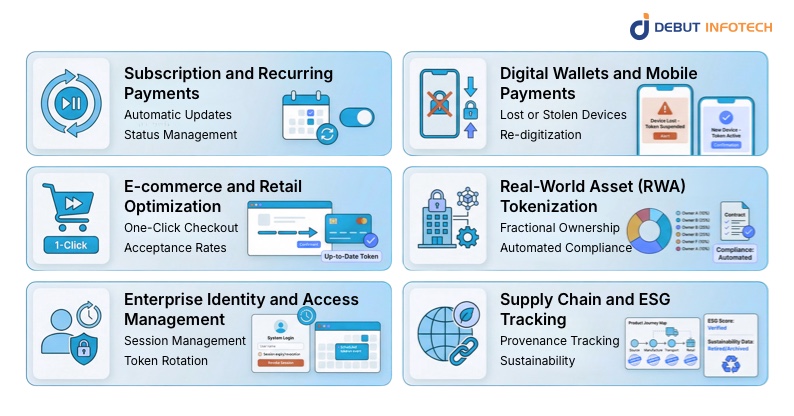
Token lifecycle management supports a wide range of real-world applications, enabling secure payments, asset tracking, identity control, and compliance across consumer, enterprise, and regulated environments.
1. Subscription and Recurring Payments
Token lifecycle management plays a central role in recurring billing models by keeping payment credentials valid over long periods. It reduces interruptions, supports automation, and ensures subscriptions continue smoothly even when underlying payment details change.
a) Automatic Updates
Automatic token updates ensure subscriptions remain active when cards expire, are reissued, or replaced. The token refreshes in the background without user input, reducing failed charges. This continuity supports predictable billing cycles, improves customer retention, and minimizes operational effort for merchants managing large subscriber bases.
b) Status Management
Status management allows tokens to be paused, resumed, or restricted in response to account changes or risk signals. If a payment issue arises, tokens can be temporarily limited rather than canceled. This flexibility helps businesses resolve issues quickly while preserving customer relationships and the value of ongoing subscriptions.
2. Digital Wallets and Mobile Payments
In mobile payment ecosystems, token lifecycle controls help balance convenience and security. Tokens enable fast, contactless transactions while allowing providers to respond quickly to device-related risks without compromising the broader user account.
a) Lost or Stolen Devices
When a device is lost or stolen, associated tokens can be suspended instantly without affecting the underlying account. This limits misuse while protecting stored credentials. Users retain confidence knowing access can be controlled remotely, reducing fraud exposure and avoiding unnecessary account replacements.
b) Re-digitization
Re-digitization allows tokens to be securely reissued to a new device after replacement or upgrade. Users regain payment functionality quickly without having to re-enter sensitive data. This process maintains continuity, reduces friction, and supports a smooth transition across devices within digital wallet environments.
3. E-commerce and Retail Optimization
Token lifecycle management strengthens online and in-store retail experiences by reducing checkout friction and improving transaction reliability. It supports faster payments while protecting customer data across repeated purchases and multiple sales channels.
a) One-Click Checkout
Tokens enable one-click checkout by securely storing payment credentials without exposing card data. Lifecycle controls ensure these tokens remain valid over time. Shoppers complete purchases faster, while merchants benefit from higher conversion rates and reduced abandonment during repeat transactions.
b) Acceptance Rates
Up-to-date tokens improve acceptance rates by preventing declines linked to expired or outdated credentials. Lifecycle updates keep payment data up to date across systems. This consistency leads to smoother authorization outcomes, fewer retries, and improved overall performance during high-volume retail transactions.
4. Real-World Asset (RWA) Tokenization
Token lifecycle management provides structure and control for representing physical or regulated assets digitally. It ensures ownership, compliance, and transfer conditions are accurately reflected throughout the asset’s digital lifespan.
a) Fractional Ownership
Lifecycle-managed tokens support fractional ownership by clearly defining issuance, transfer, and redemption rules. Each fraction remains traceable and secure. This structure allows broader participation in asset ownership while maintaining transparency, control, and accurate representation of stakeholder rights.
b) Automated Compliance
Automated compliance is enforced through lifecycle rules that restrict transfers, apply conditions, or trigger reviews. Tokens can reflect regulatory requirements in real time. This reduces manual oversight, lowers compliance risk, and ensures asset transactions remain aligned with legal obligations.
5. Enterprise Identity and Access Management (IAM)
Within enterprise environments, token lifecycle management strengthens access control by defining how identities interact with systems over time. It supports secure authentication while adapting to organizational changes and evolving risk profiles.
a) Session Management
Tokens manage user sessions by defining access duration, scope, and conditions. Lifecycle controls allow sessions to expire or be revoked automatically when risks are detected. This reduces unauthorized access while maintaining smooth workflows for authenticated users across enterprise systems.
b) Token Rotation
Token rotation replaces active tokens at defined intervals to limit long-term exposure. Regular rotation reduces the impact of compromised credentials and supports compliance requirements. This practice strengthens security posture without disrupting legitimate access or ongoing enterprise operations.
6. Supply Chain and ESG Tracking
Token lifecycle management supports transparency and accountability across supply chains and sustainability initiatives. Tokens help track assets, data, and certifications while maintaining integrity from origin through final reporting.
a) Provenance Tracking
Lifecycle-managed tokens record each stage of an asset’s journey, creating a verifiable history. Updates reflect transfers, processing, or custody changes. This traceability improves trust, reduces disputes, and supports accurate reporting across complex, multi-party supply chains.
b) Sustainability
Tokens linked to ESG data can be updated, verified, and retired as sustainability metrics change. Lifecycle controls ensure accuracy and prevent manipulation. This supports credible environmental reporting and helps organizations demonstrate measurable progress toward sustainability commitments.
7. ICO Development and Token Sale Management
Token lifecycle management plays a critical role in ICO development, governing how tokens are designed, minted, issued, restricted, and managed before, during, and after a token sale. The same lifecycle principles extend to IDOs and IEOs, where distribution mechanisms differ, but the need for controlled issuance, eligibility enforcement, and post-sale governance remains the same.
Across all token sale models, lifecycle design ensures that fundraising is not treated as a one-time issuance event. Instead, tokens are managed as long-lived digital instruments, with rules that preserve supply integrity, investor protections, and regulatory alignment throughout their usable lifespan.
a) Controlled Token Issuance
In ICO development, lifecycle rules define how minted tokens are released into circulation based on predefined eligibility criteria. This includes KYC and KYB checks, accreditation status where applicable, jurisdictional restrictions, and wallet verification.
The same controlled issuance logic applies to IDOs and IEOs, even when distribution is mediated through decentralized platforms or centralized exchanges. These controls prevent unauthorized participation, limit regulatory exposure, and ensure tokens enter circulation only under approved conditions.
b) Vesting, Lock-Ups, and Allocation Controls
Token lifecycle logic enables automated vesting schedules, lock-up periods, and conditional release mechanisms for investors, founders, advisors, and ecosystem participants. These controls reduce market volatility, discourage speculative dumping, and enforce transparent allocation management after the token sale concludes.
Whether tokens are distributed via an ICO, IDO, or IEO, lifecycle-enforced vesting ensures predictable supply release and supports long-term market stability.
c) Post-Sale Governance and Ongoing Compliance
After the token sale phase, lifecycle management supports transfer restrictions, state transitions, auditability, and regulatory reporting as obligations evolve. Tokens may require restrictions based on jurisdiction, trading venue, or regulatory status, even after initial distribution.
Lifecycle controls ensure tokens remain compliant, traceable, and operational well beyond the fundraising event, supporting secondary trading, platform utility, and long-term ecosystem growth without compromising governance or security.
Partner With Token Experts
Token development is not just about generation. We handle the full lifecycle so your product runs smoothly, stays secure, and grows without technical debt.
Challenges in Token Lifecycle Management
While crypto token lifecycle management delivers strong security and operational benefits, implementing and maintaining it introduces technical, regulatory, and usability challenges that organizations must address to ensure reliability, compliance, and long-term effectiveness
1. Technical and Operational Challenges
Implementing token lifecycle systems often requires deep integration with legacy platforms, payment networks, and identity services. Managing scalability, latency, and reliability across multiple environments adds complexity. Operational teams must also handle monitoring, updates, and exception handling without disrupting active tokens or core business processes.
2. Security and Risk Management
Tokens reduce exposure to sensitive data, but poor governance can introduce new risks. Weak access controls, delayed revocation, or misconfigured policies may allow misuse. Effective lifecycle management demands continuous monitoring, rapid response mechanisms, and well-defined escalation paths to maintain trust and system integrity.
3. Regulatory and Legal Hurdles
Token economy and usage must comply with data protection, financial, and industry-specific regulations across jurisdictions. Requirements around data residency, auditability, and consent can complicate implementation. Organizations must align token lifetime policies with evolving regulatory expectations while maintaining consistent token behavior across markets and operational regions.
4. Market and User Experience Issues
Strong security controls can introduce friction if poorly designed. Frequent re-authentication, token errors, or failed updates may frustrate users. Balancing protection with usability requires careful lifecycle planning, clear communication, and reliable automation that minimizes visible disruptions while preserving a smooth overall experience.
Partner with Debut Infotech for End-to-End Token Lifecycle Engineering
At Debut Infotech, token development goes far beyond creation or issuance. We work at the practical end of token lifecycle management, where architecture decisions, security controls, and long-term usability define whether a token system succeeds in real-world environments.
Our teams design and implement token infrastructures that account for the entire lifecycle — from minting and controlled issuance to updates, state transitions, rotation, and retirement. This lifecycle-first approach ensures tokens remain secure, compliant, and operational as products scale, regulations evolve, and business models mature.
We apply this expertise across a broad range of tokenization initiatives, supporting organizations with end-to-end crypto token development services, including:
- ERC20 Token Development for fungible utility and governance tokens
- BEP20 Token Development for scalable, cost-efficient ecosystems
- Meme Coin Development with structured tokenomics and controlled supply models
- Stablecoin Development backed by transparent reserves, compliance logic, and lifecycle controls
Each token solution is designed with real-world use cases in mind — whether for payments, identity, asset tokenization, fundraising, or platform utility ensuring lifecycle discipline is built in from day one.
For enterprises looking to design, build, or extend robust token-based platforms, partner with Debut Infotech and hire blockchain developers to design, implement, and operate token lifecycles that reduce execution risk, simplify compliance, and support sustainable growth from day one.
FAQs
The lifecycle of a token covers everything from creation to retirement. It starts when a token is generated, then moves through activation, regular use, possible suspension, renewal, and finally deletion. Each stage controls how the token can be used, secured, monitored, and eventually removed from active systems.
Token provisioning is the process of issuing a token and linking it to the original data it represents. The system validates the request, generates the token, applies usage rules, sets expiry limits, and securely stores mappings. Once provisioned, the token is ready for controlled use.
A suspended token is temporarily disabled, while a deleted token is permanently removed. Suspension keeps the token data intact and allows reactivation later. Deletion wipes the token from the system, breaks all links, and prevents any future use under any circumstance across all connected platforms and services.
When a token is deleted, it becomes unusable immediately. Any system relying on it will reject requests tied to that token. Logs may still exist for audits, but the token itself cannot be recovered, reactivated, or reused in any workflow after it is deleted at the platform level.
Tokens often have longer expiry because they reduce exposure to sensitive data. If compromised, tokens can be revoked without replacing the underlying card. This added control, along with usage limits and scope restrictions, allows tokens to stay valid longer without increasing overall risk for merchants and platforms.
Security checks vary by stage. Creation includes identity and permission validation. Active tokens are monitored for misuse, scope limits, and access patterns. Suspension triggers anomaly checks. Renewal involves revalidation. Deletion enforces revocation and audit logging to confirm that the token cannot be accessed.
At scale, token lifecycle management relies on automation. Systems track token states, apply rules programmatically, rotate tokens in batches, and revoke access instantly when needed. Centralized monitoring, logging, and policy enforcement reduce manual work and help teams manage millions of tokens without errors.
Our Latest Insights




